Mass Deployment of the Chrome Extension for Gmail¶
For users of the Email Sidebar on:

6 min read
RGES Chrome Extension for Gmail includes most of RGES Outlook Add-In’s and Synchronization features for Gmail / Google Workspace (G Suite). The Extension can be installed individually or mass-deployed for all end users by the local mail server Admin.
This article describes the mass deployment scenario where the local mail server Admin installs the RGES for Gmail and Salesforce Chrome Extension for all RGES end users in an Org. It is a standard secure Chrome browser extension reviewed by Google, and in the enterprise environment it can be mass-deployed for multiple end users using Microsoft Group Policy mechanisms. This Chrome Extension mass deployment method is only viable in Windows systems, Windows Active Directory environment.
The alternative method for non-Windows systems uses Google’s native mechanisms which ensure automatic Extensions installation in Chrome browser after that was enforced for logged in Google accounts by Google Workplace Admin. See this Google article for complete information.
Besides Extension installation, mass RG Email Sidebar for Gmail deployment requires mass Sync activation via a Service account. See this article to learn how to do that.
To mass-deploy the Chrome Extension using Active Directory, follow the instruction below (based on the guidelines developed by Dennis Span).
RG Email Sidebar Extension deployment string to be used (fast prod build installation): agfekjndkedoakoeahndfnjilkifbicn;https://clients2.google.com/service/update2/crx
1. Import the Google Chrome ADMX files into your Active Directory environment
The described method to mass-deploy Chrome extensions is through Microsoft Group Policy. As per Google: “For Windows, it is recommended to use Group Policy vs. preferences files because only Group Policy can be enforced”. An identical statement is made in the Chrome Deployment Guide: “Use Windows Group Policies (GPO policies) and cloud policy over preferences when possible. Unlike policies, preferences do not apply to previous installations of Chrome and are only applied to a single profile. Policies also override any preferences settings for a feature. Also note that the master_preferences file can be changed and not enforced like group policies can”.
Google provides official ADM and ADMX files which enable the end users to manage its products. For RGES Extension mass deployment, we recommend you to use the ADMX files only and not the ADM files. Before you can use Microsoft Group Policies to mass-deploy the Extension, you first need to import the Google Chrome ADMX files in your Group Policy Central Store. The ADMX files, as well as the ADM language files, (.ADML) can be found in the directory Configuration\admx* of the extracted Chrome Enterprise Bundle archive.
If you are not familiar with the Central Store for Group Policies and require more detailed information, refer to the official Microsoft article How to create and manage the Central Store for Group Policy Administrative Templates in Windows.
Chrome Enterprise Bundle includes the following six ADMX files:
- chrome.admx
- ChromeUASwitcher.admx
- google.admx
- GoogleUpdate.admx
- LegacyBrowserSupport.admx
- PasswordAlert.admx
The purposes of most of these ADMX files are self-explanatory, except for the ADMX file google.admx. This file only has one purpose, which is to set the shared “Google” folder in the Group Policy editor. This folder ensures that all Google policy settings (for the Chrome browser or other Google products) are grouped under one folder.

The Group Policy Central Store is located on your domain controllers.
- The Central Store root path (containing the ADMX files): \\%LogonServer%\sysvol\#DomainName#\Policies\PolicyDefinitions
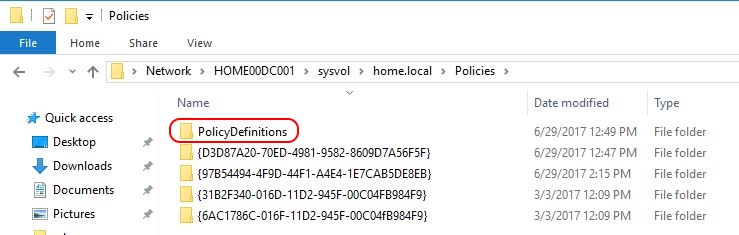
The ADMX files are put in the root of the Store; the language files (*.ADML), are put in the language-specific subdirectories.
- Central Store subdirectories for the language files: \\%LogonServer%\sysvol\#DomainName#\Policies\PolicyDefinitions\#languagecode-countrycode#
Copy the Chrome ADMX files into this folder:
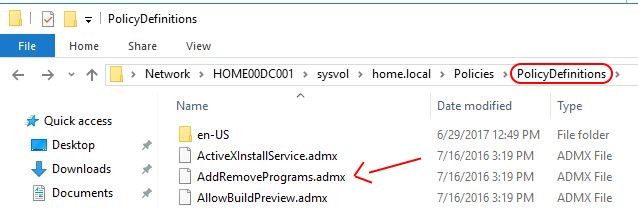
Copy the English language .ADML files into the en-US folder:

Note
The 2021 updates of RG Email Sidebar also include support for several more languages; make sure to copy non-English ADML files for the supported language(s) you will use into their corresponding directories. The correct directory name for your language can be found in Configuration\admx of the unarchived Chrome Enterprise Bundle
Now that you have copied all required files, you can start configuring your settings using a Group Policy editor (such as Group Policy Management Console).
In case you do not want to update your Central Store right away, you can first perform some tests by using the local ADMX repository on a server. The local repository of a Windows server is located here: C:\Windows\PolicyDefinitions. Apply the same procedure for copying the ADMX and ADML files as for the Central Store. Use the local Group Policy editor to configure your settings (gpedit.msc).
Important
The future versions of Chrome will feature updated .ADMX and .ADML files included into Chrome Enterprise Bundle. Please remember that your Group Policy settings are not affected when you update the .ADMX files. Your settings are kept in different files within each individual Group Policy itself: Registry.pol contains the Group Policy settings; .xml (e.g. Files.xml*) contains your Group Policy preferences settings
The path to an individual group policy is as follows: \\%LogonServer%\sysvol\#DomainName#\Policies\#PolicyGUID#
After configuring your Chrome settings you can check if your Chrome policies are applied by entering chrome://policy in Chrome address bar. This will show you all Chrome settings applied for your PC and user.
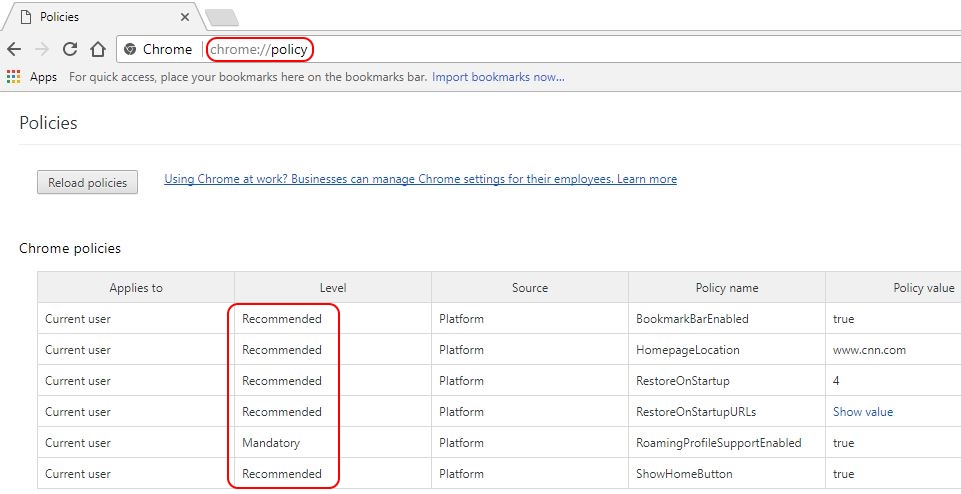
User settings can be either mandatory or recommended. Mandatory user settings are configured here:
User Configuration \ Administrative Templates \ Google \ Google Chrome
Recommended user settings are configured here:
User Configuration \ Administrative Templates \ Google \ Google Chrome - Default Settings (users can override)
On the local server or client, Chrome’s computer and user policies are stored in the following registry keys:
- HKEY_CURRENT_USER \ SOFTWARE \ Policies \ Google \ Chrome
- HKEY_LOCAL_MACHINE \ SOFTWARE \ Policies \ Google \ Chrome
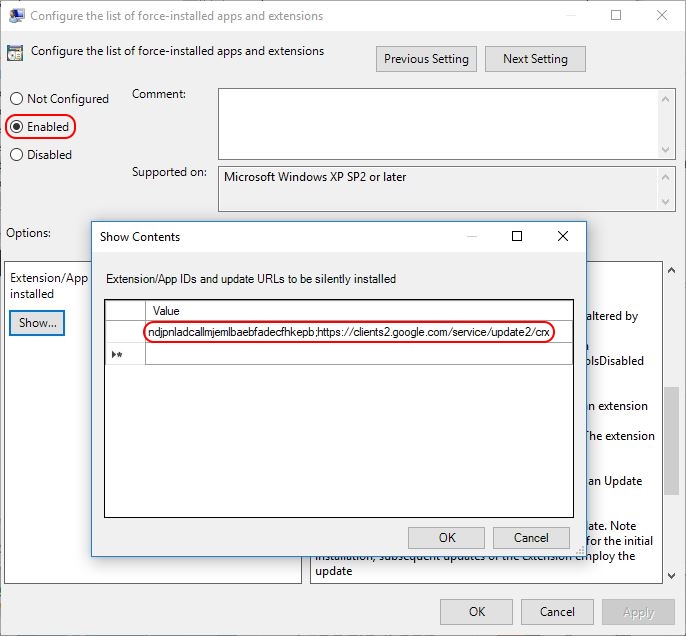
2. To force-install RGES for Salesforce and Gmail Chrome Extension, open your Group Policy Management Console (dsa.msc) and go to User Configuration > Administrative Templates > Google > Google Chrome > Extensions. Fine the setting Configure the list of force-installed apps and extensions and enable it.
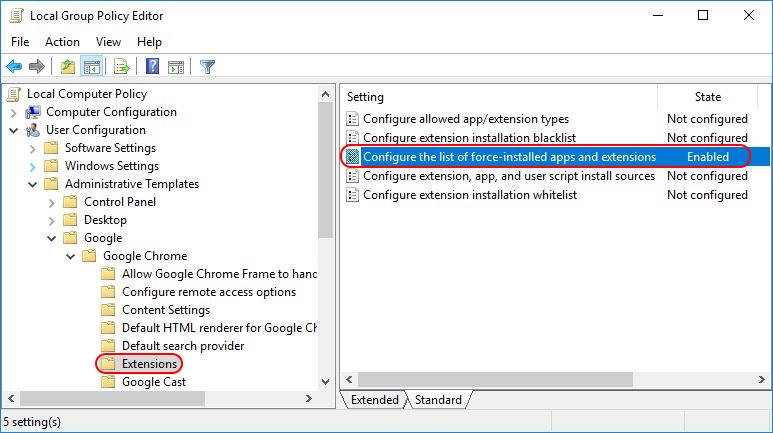
Click Show and enter the string we provided at the beginning of the article into the Value field:
agfekjndkedoakoeahndfnjilkifbicn;https://clients2.google.com/service/update2/crx
Now the policy setting is configured. On the next Group Policy refresh the users will automatically get the required extension. To summarize, this policy update will mass-deploy the Extension for all users to whom the Group Policy applies. Extension installation is performed silently, without user interaction.
As mentioned above, after the Extension has been mass-deployed, you can see it in the directory on the users’ PCs C:\Users\%UserName%\AppData\Local\Google\Chrome\User Data\Default\Extensions
!!! note “Note” Make sure that Developer mode is disabled on the Extensions tab of users’ Chrome browsers. During the tests, Extensions were not automatically installed with Developer mode enabled
Extension removal¶
If you delete the Extension from the Configure the list of force-installed apps and extensions policy setting, the extension is automatically removed from Chrome browser for all users to whom the Group Policy applies.
Future updates of the RGES for Salesforce and Gmail Extension are automatically installed through the update URL specified in the Extension’s manifest file (https://clients2.google.com/service/update2/crx).
RGES Extension log on after deployment¶
After the Extension was deployed, the end users should log on to RG Email Sidebar individually via the Extension’s Sidebar – see this article for more information.

We would love to hear from you!